For industrial leaders, data has become the new oil—but with a critical flaw. It’s often locked in isolated, proprietary vaults, its full value untapped due to legitimate fears of exposing intellectual property, sensitive operational patterns, or customer information. The dilemma is stark: collaborate with partners and AI to unlock transformative insights, or hoard data to maintain security and competitive edge. This standoff is now ending. The convergence of Privacy-Enhancing Technologies (PETs) and modern Large Language Models (LLMs) is forging a new paradigm: secure, collaborative intelligence without compromise.

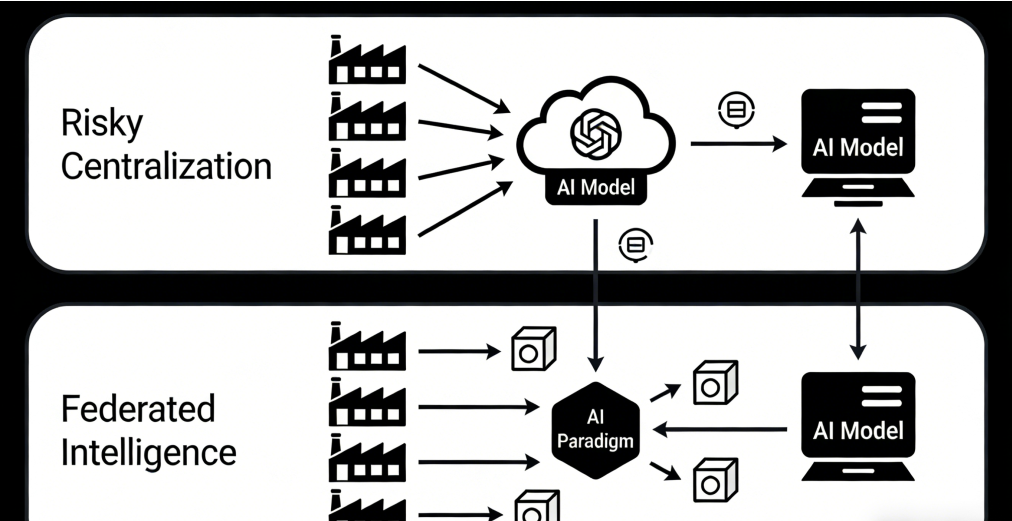
The core challenge is the “data usability paradox.” Traditional analytics and AI require raw data to be pooled or copied, creating unacceptable exposure risks. Privacy Computing—encompassing Federated Learning, Secure Multi-Party Computation (MPC), and Homomorphic Encryption—solves this by enabling computation on data that remains encrypted or distributed. Think of it as a secure, virtual boardroom. Multiple companies can bring their confidential data (like supply chain logs, component failure rates, or energy consumption patterns) to the table. Through cryptographic protocols, they can jointly train a model or run complex queries to discover cross-organizational insights, but no participant ever sees another’s raw data. The data is usable but remains invisible outside its origin.
This is powerful alone, but its synergy with next-generation LLMs is revolutionary. Modern enterprise-grade LLMs are no longer just text generators; they are sophisticated reasoning engines capable of complex analysis, pattern recognition, and logical inference. When PETs create a secure channel for these models to access distributed, sensitive data, they become the ultimate confidential analyst.
Consider the practical applications reshaping industrial strategy:
- Secure Supply Chain Optimization: A manufacturer, its key suppliers, and its logistics partner can employ a federated learning framework. Each party retains its private data on costs, capacities, and delays. An LLM-powered model, trained across this federated network, can identify systemic bottlenecks, predict disruptions, and propose resilient re-routing strategies—all without any party disclosing its pricing, internal capacity, or contractual terms. The intelligence is shared; the competitive data is not.
- Cross-Industry Predictive Maintenance Consortium: Competing automotive OEMs could form a consortium to improve reliability for a common, safety-critical component. Using Secure MPC, they can pool encrypted, anonymized sensor data from millions of vehicle miles. A specialized LLM can analyze this vast, privacy-protected dataset to identify subtle, pre-failure signatures no single company could detect alone, leading to safer products and reduced warranty costs for all, without transferring core engineering data.
- Confidential R&D Collaboration: In pharmaceuticals or advanced materials, research consortia can use homomorphic encryption. Partner A can submit an encrypted molecular structure to Partner B’s proprietary AI simulation model. The model runs its analysis on the encrypted input and returns an encrypted result—only Partner A can decrypt it. The model’s intellectual property and the specific compound design both remain fully protected, accelerating innovation safely.
The strategic advantage is profound. This is not just an IT solution; it is a new model for competitive cooperation. It allows you to participate in and leverage collective intelligence ecosystems while maintaining sovereign control over your core data assets. It turns data protection from a compliance cost center into an enabler of high-value collaboration.
Implementing this requires a shift in architecture. The focus moves from building centralized data lakes to deploying “intelligence mesh” networks with standardized PET protocols and AI containers that can be deployed at the edge of partner firewalls. Leaders like IBM, Intel, and specialized firms are offering trusted execution environments (TEEs) and software frameworks that make this increasingly operational.
As the CEO of a global industrial conglomerate recently noted, “This technology fundamentally alters the risk calculus. We can now envision a future where our most sensitive operational data fuels AI-driven optimization across our entire value chain—with partners, with customers—without ever leaving our direct control. It dissolves the trade-off between security and insight.”
The trajectory is toward Autonomous, Confidential Operations. The future industrial AI will not only recommend actions but will execute them—negotiating dynamic pricing, adjusting just-in-time inventory orders, optimizing energy bids—by continuously analyzing live, encrypted data streams from across a trusted network.
For the industrial executive, the message is clear. The fusion of Privacy Computing and Advanced AI is the key to unlocking the next frontier of efficiency, innovation, and resilience. It resolves the core tension of the digital age. Your data vaults are no longer just defensive fortresses; they are now the secure portals to a collaborative, intelligent, and supremely competitive future.






Discuss